Shoviv Exchange Server Suite is a bunch of key tools which Exchange server /Helpdesk admin must have handy. This suite can rescue Admins from critical issues which they can encounter as part of the day-to-day operations. Below are some of the high-level functions of the Shoviv Exchange Server Suite.
It offers some great features like
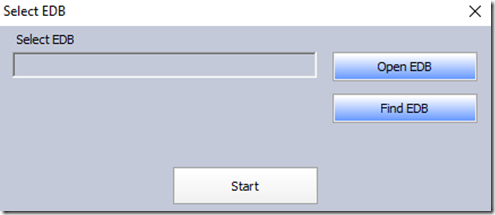
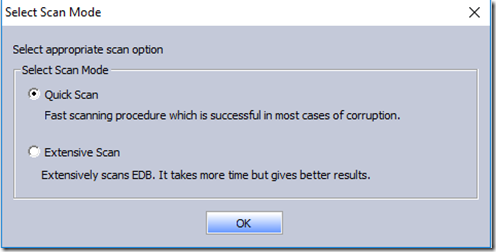
Recovers corrupted EDB, OST, and PST Files
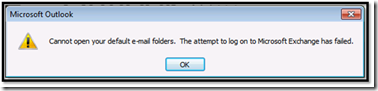
Corruption of EDB is not very common but if it happens then you are in deep trouble. It takes ages to repair an EDB file. Quick recovery would be to create a dial tone mailbox so users can access send/receive new emails then use Shoviv Exchange Server Suite to restore the EDB contents to the user’s PST. You could also use it to recover the corrupted PST/OST content to the new one.
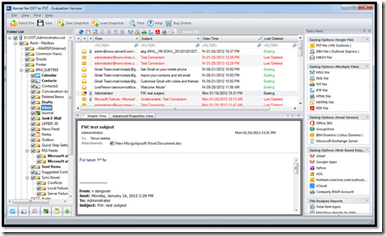
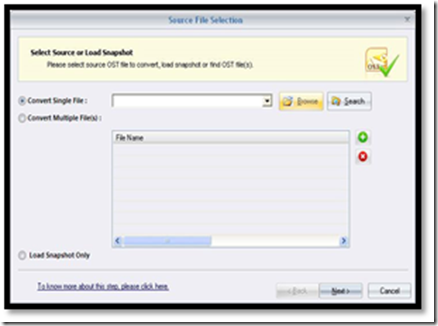
Exports OST file content to Outlook PST, Exchange Server, or even Office 365 mailbox(es)
Outlook Data file OST is to use the store to the offline synchronized copy of your mailbox information on your local computer. This allows users to continue to access email when they are not connected to the network and it also reduces the load on the exchange/network by making connect to Exchange one regular internal and not connected all the times. These features allow users to export the content of the OST file to PST or event directly to the Exchange /office 365 mailbox(es).
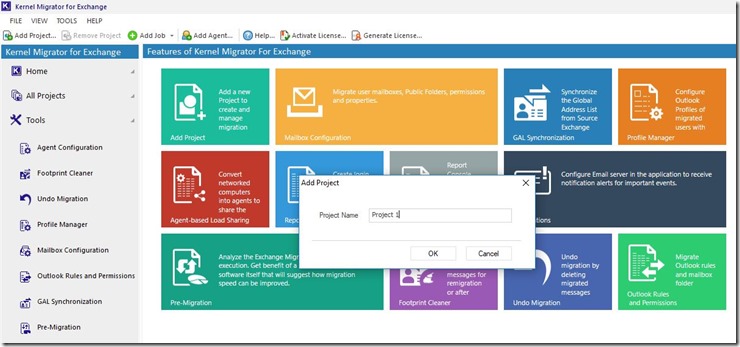
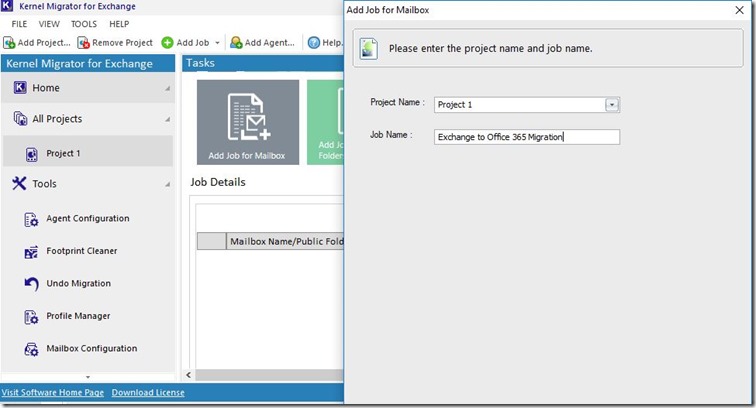
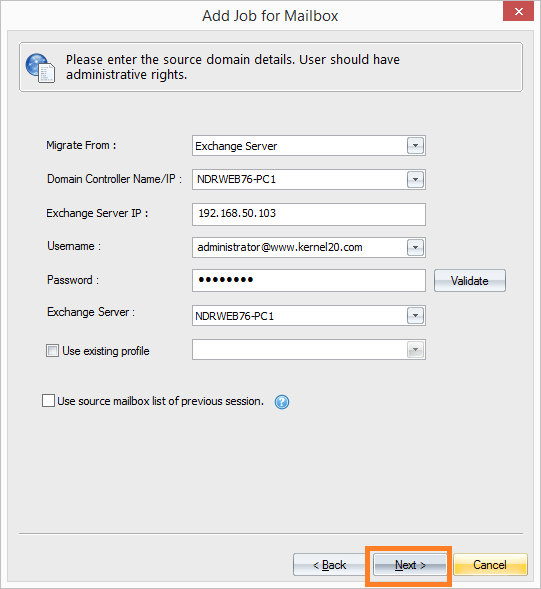
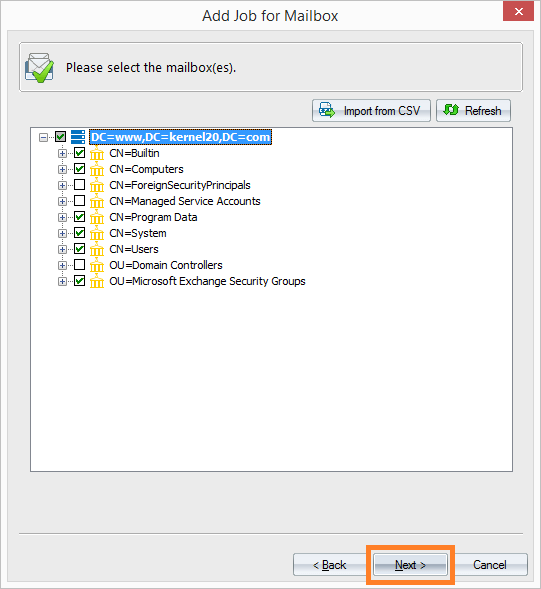
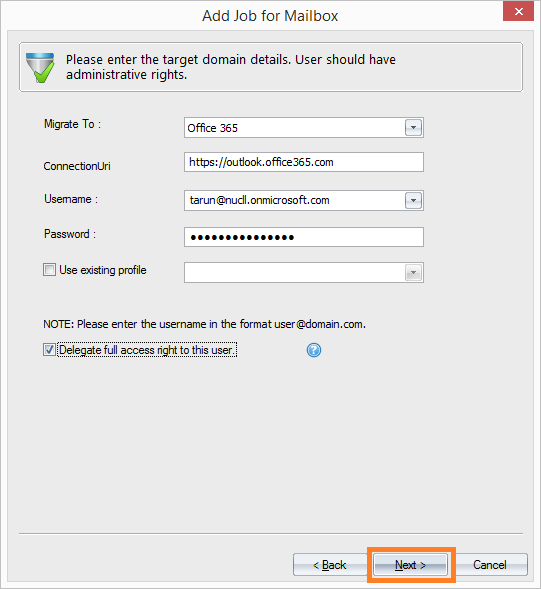
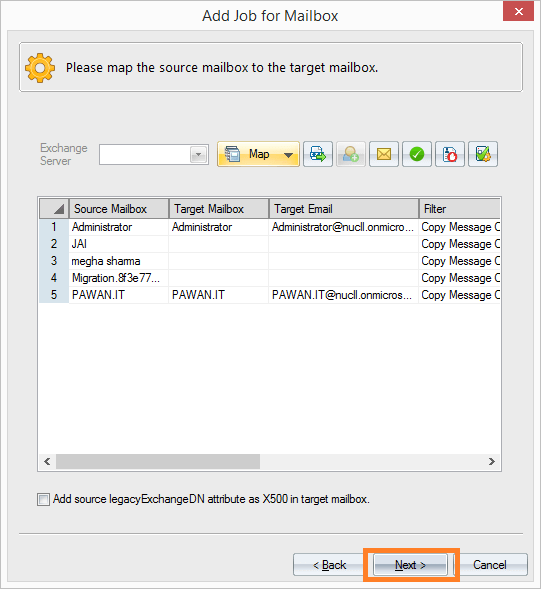
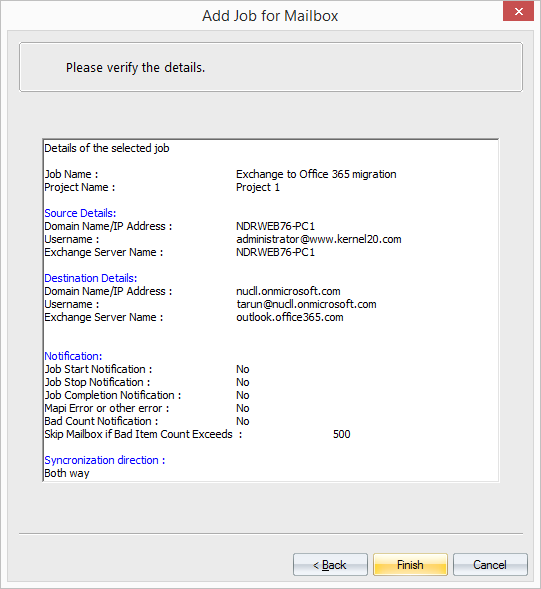
Migrate the content of Exchange mailbox to Office 365 mailbox and vice-versa
While migrating the mailboxes from one version of Exchange to another E.g. You cannot upgrade to Exchange 2019 directly from Exchange 2010 and need to follow two-step approaches. First, migrate from Exchange 2010 to Exchange 2013/2016. Then Migrate to Exchange 2019 from Exchange 2013/2016. To avoid these two steps approach it needs to spin out a new Exchange organization with Exchange 2019 and use Shoviv Exchange Server Suite to export all the content from exchange 2010 to Exchange 2019 mailbox directly.
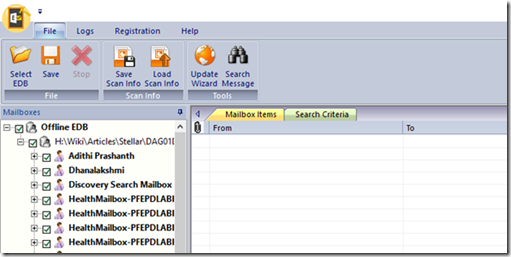
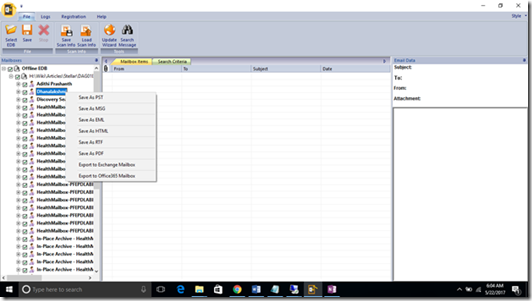
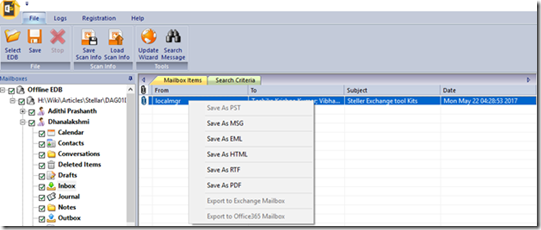
Export the contents of Mailboxes from EDB to Outlook PST /Exchange / Office 365 mailbox(es) directly.
This feature allows admins to Export the content of the EDB to users’ PST files or connects to another exchange server/office 365. Eg. There are scenarios where a company gets acquired / merges. This can happen so quickly and the admin may not have time to merge the Exchange Org and do the co-existence to perform graceful migration. The simplest and quick solution is to provision a new mailbox for all the users in the parent exchange organization then copy the EDB files to the parent Exchange org and then export the content directly to the target mailbox.
Import PST Files into Live Exchange and Office 365 Mailboxes.
Many organizations have a PST culture and allow users to create the PST on their workstations and some organizations don’t allow PST at all. If you have the requirement to import Mulitple PST to mailboxes then you will have a challenge. You need Exchange and PowerShell skills to automate this process. This change can be easily addressed using the Shoviv Exchange Server Suite
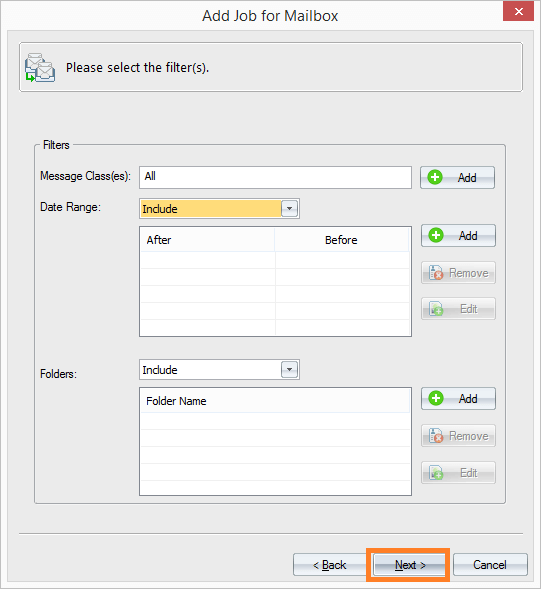
Advances search and filter to find the required message and export the contents
This is can be a great tool for the Legal / Compliance /Cyber depart of the organizations. Native out-of-box Exchange mailbox export offers limited functionality and but this tool can be used to search and export the specific mail items only with the specific message class, item dates, etc.
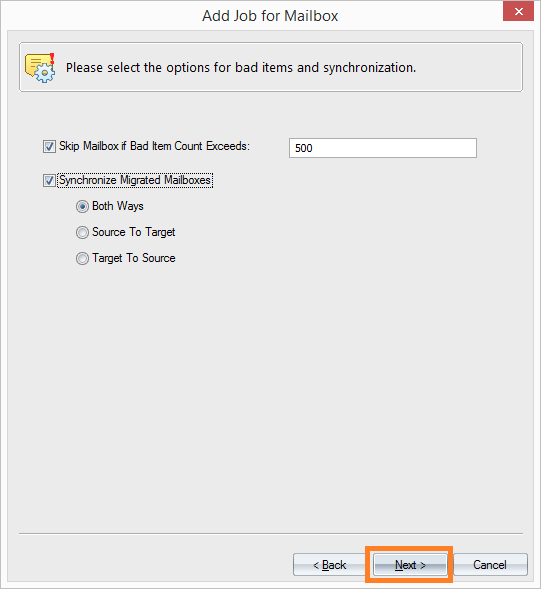
Incremental Export/Backup in PST files/Live Exchange/Office 365 Mailbox(es)
The incremental backup/export is a great time saver and deduplication option. Eg. users can have a situation where they need to backup/export the mailbox content in multiple date intervals. Here the incremental backup/export option allows the software to skips already exported items and prevents duplicity while processing again. Besides this, the Export and backup process depends on the internet connection, and if a sudden network issue occurs, then the migration process gets stuck. In this scenario, the incremental option comes in handy to resume the migration process.I would recommend this tool for any organization. It offers great features to address many day-to-day operations and critical scenarios. I have seen many bad days with Exchange and when it hits it can be a disaster. Shoviv Exchange Server Suite will change the way you handle many scenarios. It reduces tons of effort and time to allow you to focus on the thing that matters.